Trojan - aims to be H magazine photos
Computer Emergency Response Team UNAM-CERT received an email that contained a download link of a potential malware. Below is the email message that refers to fake pictures of the H magazine:
The link leads to the download of "Ninel_Conde_Revista_H_.zip", a file hosted in a server located in the United States.

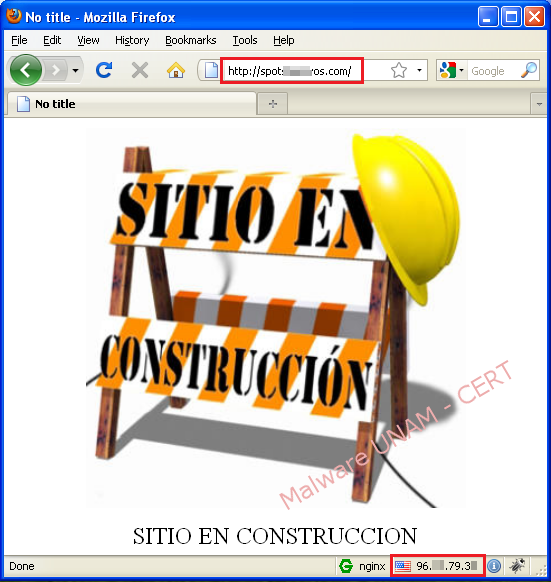
The landing page of the website that hosts the ZIP file shows an image with the caption: "SITIO EN CONSTRUCCIÓN" (SITE UNDER CONSTRUCTION), therefore, UNAM-CERT was unable to determinate whether it’s an official site that was committed or if it's used to propagate suspicious files.
When unzipping file "Ninel_Conde_Revista_H_.zip", it's obtained the "Ninel Conde Revista H.exe" executable. In a controlled environment without access to Internet, the exe file shows the following behavior:
- The "web0413.exe" process starts up, which in turn starts "itacoffe.exe" process.

- Immediately after, the "Ninel Conde Revista H.exe" process launches "Ninel.exe" process, and the program in execution "itacoffe.exe" launches "url.exe".

- The "url.exe" process attempt to establish connection to a web server by port 80, as it’s shown below in network traffic:
- After a few seconds, a maximized window appears in the infected computer with the name "Ninel Conde, El bombon Asesino" (Ninel Conde, The Murderer marshmallow). It also warns that "webagent.exe" file was not found.

- The Registry activity shows that the "itacofee" key is created, which starts at every system reboot the "webagent.exe" executable file, which is not generated after executing the original sample.
- About the file system, the malware creates two folders: "itacoffee" and "tmp":

- In the image below, the created files in the two folders mentioned above are shown:


By making a strings analysis, it was found that the web address "http://nsis.sf.net", where the "Nullsoft Scriptable Install System" tool can be downloaded from, which is used to create installers for Windows operating systems.

This installer was also identified with "Exeinfo PE" tool.

By providing Internet connection to the sample, it was determined the following behavior:
- The "javaw.exe" process was started and it established network connection to a remote web server using IP address.

- The process is not the user Java application, but is a running program that is downloaded once the malware sample obtains interaction with the Internet.

- In network traffic, it was identified that a request is made, by GET method, to download the "webagent.zip" file.
- Once the download of the compressed ZIP file of 52 MB is completed, the "zip.exe" process is launched, such action leads to decompress the file that was downloaded. Once extracted all files and folders, the "webagent.exe" process is started up.

- "webagent.exe"is the same process that was referenced by the registry key, whom was created when the "Ninel Conde H.exe" sample was executed and that the maximized interface also couldn’t find.

- Below the files contained in the "webagent.zip" file are shown.

- It is also shown in network traffic that some requests are made to another remote server path, where the MAC address of the infected system is sent in the variable "mac".
- The above action could be carried out in order to keep track of infected computers and know which settings to apply whenever the sample process is started up.
During the analysis for this particular sample, it has a set of discharges from files that are being downloaded and running in order to not to be detected as malicious by the antivirus engines, the behavior depends on what the creator of the malicious sample sends in requested downloads.